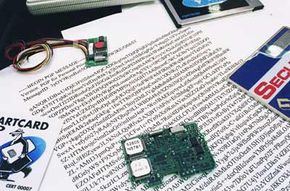
Security Encryption Systems
Computer encryption is based on the science ofcryptography, which has been used as long as humans have wanted to keep information secret. Before the digital age, the biggest users of cryptography were governments, particularly for military purposes.
The Greek historian Plutarch wrote, for example, about Spartan generals who sent and received sensitive messages using ascytale, a thin cylinder made out of wood. The general would wrap a piece of parchment around the scytale and write his message along its length. When someone removed the paper from the cylinder, the writing appeared to be a jumble of nonsense. But if the other general receiving the parchment had a scytale of similar size, he could wrap the paper around it and easily read the intended message.
Advertisement
The Greeks were also the first to use ciphers, specific codes that involve substitutions or transpositions of letters and numbers.
As long as both generals had the correct cipher, they could decode any message the other sent. To make the message more difficult to decipher, they could arrange the letters inside the grid in any combination.
大多数形式的加密使用these days rely oncomputers, simply because a human-based code is too easy for a computer to crack. Ciphers are also better known today asalgorithms, which are the guides for encryption -- they provide a way in which to craft a message and give a certain range of possible combinations. Akey, on the other hand, helps a person or computer figure out the one possibility on a given occasion.
Computer encryption systems generally belong in one of two categories:
- Symmetric-key encryption
- Public-key encryption
In the following sections, you'll learn about each of these systems.